There are certain occurrences in life that are unfortunate. They just are. Having your house broken into. Crashing your car into a telephone pole. Burning up half your lawn during a bonfire. No matter who you are, any one of these things happening to you would be unfortunate.
However, there are some people for which these unfortunate occurrences would be absolutely, positively terrible. It’s one thing to have your house broken into as an average person, but what if you made your living as a home security expert? Or what if you were a driving instructor that crashed your car into a pole? Or a firefighter that burned up your lawn?
There’s unfortunate, and then there’s unfortunate and embarrassingly ironic. Which brings us to the story of the large-scale DDoS attack on GitHub.
What you have to get about GitHub
GitHub.com is a web-based hosting service dedicated to giving software developers a convenient place to store and work on their projects, as well as open their projects up to collaboration. The beauty of GitHub is that it stores every single change and revision made to each project, and provides change logs that keep track of who made what change and when they did so.
Not only does this make it easy to provide updates, but it also makes it virtually impossible to irreparably mess up anything. It’s no wonder GitHub reportedly has over 9 million registered users.
An unlikely target that was nevertheless targeted
So let’s get this straight: GitHub is a website populated by some of the smartest, most tech-savvy people on the internet. Millions of them. And yet, GitHub just crawled out from under a massive five-day DDoS attack reportedly perpetrated by the Chinese government to censor pages they did not want available to Chinese citizens.
GitHub themselves described the DDoS attack as the largest they’d ever seen. In addition to being slammed with multiple known DDoS attack vectors, they were also hit with what they called new and complex techniques that involved sending unsuspecting and uninvolved web users to GitHub, flooding the website with traffic. Specifically, users of the Chinese search engine Baidu were redirected to a GitHub page mirroring the New York Times Chinese language version for the people of China, and a GitHub page run by GreatFire.org that links to copies of ten websites that are currently blocked in China.
The experts weigh in on the attackers
For their part, the Chinese government has sort of denied but not truly denied their involvement, instead opting to remind the world that China is one of the major victims of cyber attacks. Baidu outright denied that their services had what they referred to as “security problems” or “hacker attacks.”
However, this is at odds with what internet security experts are saying. GreatFire posted a forensic report from an independent security researcher that examined evidence from the attack and identified the Cyberspace Administration of China as the culprit.
Ofer Gayer, a security researcher at DDoS mitigation firm Incapsula, seems to share this opinion. “You need to have good control over infrastructure to mount an attack like this,” he said. “The Chinese have control of the infrastructure of an entire country, so they can divert traffic to wherever they want, inject code they want to run, and create requests with the code to GitHub.”
Gayer also went on to explain why this particular DDoS attack would have been harder to mitigate compared to more standard DDoS attacks that use botnets. “With botnets, all the requests look pretty much the same, so once patterns are identified, you can block them,” he said. “In this case, it’s very diverse. You have many different IPs and browsers creating non-homogenous traffic. This attack is very clever, and it’s not very easy to mitigate.”
What it all means
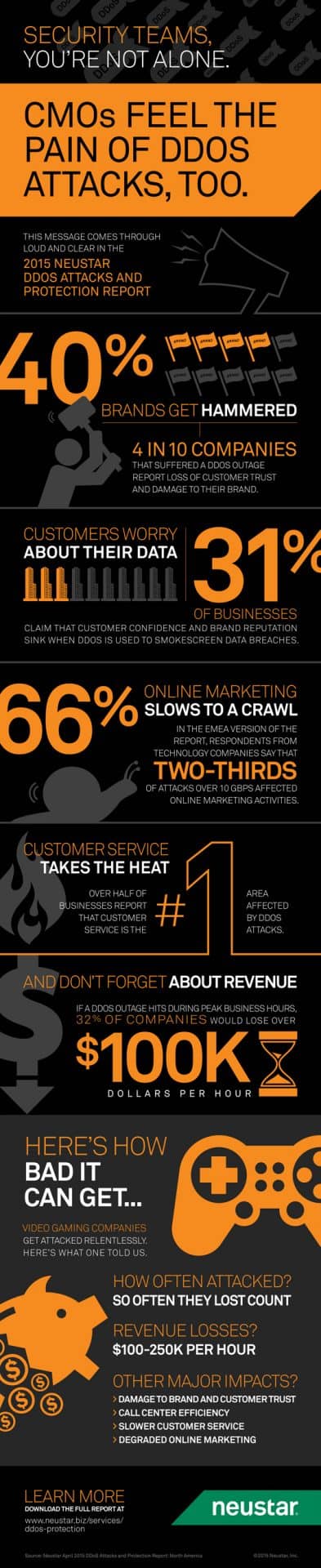
This is definitely a case of if it can happen to them, it can happen to anyone. If a website full of tech experts like GitHub isn’t prepared to deal with a DDoS attack, then it’s likely no website can be – unless it has professional DDoS protection.
This is the third high-profile DDoS attack where a nation’s government was rumoured to be involved. With DDoS attacks now coming from hackers, legitimate organizations and even governments, there’s an increasing number of attacks with increasingly complex techniques and increasingly devastating consequences. If GitHub wasn’t prepared to deal with this reality, are you?’