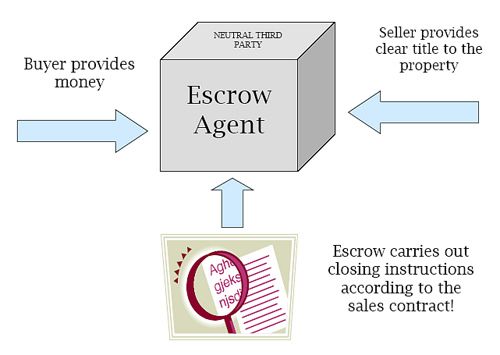
When it comes to providing many forms of technology, such as services, escrow can prove invaluable. It’s a simple argument: when dealing with licensed services, virtually everyone is looking to protect themselves against any risk.
Escrow, to put it simply, is just useful at both ends of the deal. For customers, it encourages trust and commitment, while providers can use it to show they are serious about their product. As a tech service provider, it’s likely you fall into both categories: on one hand, you have customers to provide your own digital services to but, at the same time it’s likely there are certain pieces of software you yourself might depend on.
Proactive Protection
While escrow is used to offer a quick resolution in disputes over software as a service, its instant benefit is much more proactive. Using such a service puts the provider at risk of losing their code if they fail to meet their end of the software as a service agreement and, when the actual software itself is on the line, there is little else that compares in pure motivation to provide a working product.
For a tech service provider, this offers the exact image you want. It suggests you are capable of delivering and, as such, are even willing to put your material on the line. Doing so demonstrates confidence to customers, which is never a bad thing to have associated with your name and service.
How do I know it’s the real code?
Of course, the one problem with escrow is that you can’t access what’s inside when you want to. It’s one to have the code put in there, but how do you know it’s the actual source code that you need?
Well, since you can’t access the code you should rely on the only party that can do so and remain honest at the same time – not all agencies provide such services but some, such as NCC Group, specialise in it.
Typically, this process will come in the form of a detailed report, confirming that the relevant scripts and pieces of code are there – it’s one thing to know most of it is there but ‘most’ won’t provide a working product.
Instead, some agencies actually test the code, building up from the code alone, detailing their findings into a comprehensive report. Not only does this verify the end result of the code available for escrow, thus validating the account, it provides instructions.
Should you ever acquire this code, this document will subsequently prove invaluable to your IT department or expertise.

