Saving time on any project is the key to making the project as efficient as possible. Efficiency is essential to the production process, and at the end of the day, it’s going to save you money. When you’re designing a website, app, or software application, it’s important to use a good wireframing tool to save you time on the design process. Here’s how a wireframe can help.
1. Setting The Groundwork
Any building project starts with one very important item: a blueprint. Buildings, bridges, and even roads all start with a design on paper. This helps the designers iron out the details and get things just right before moving to the building phase.
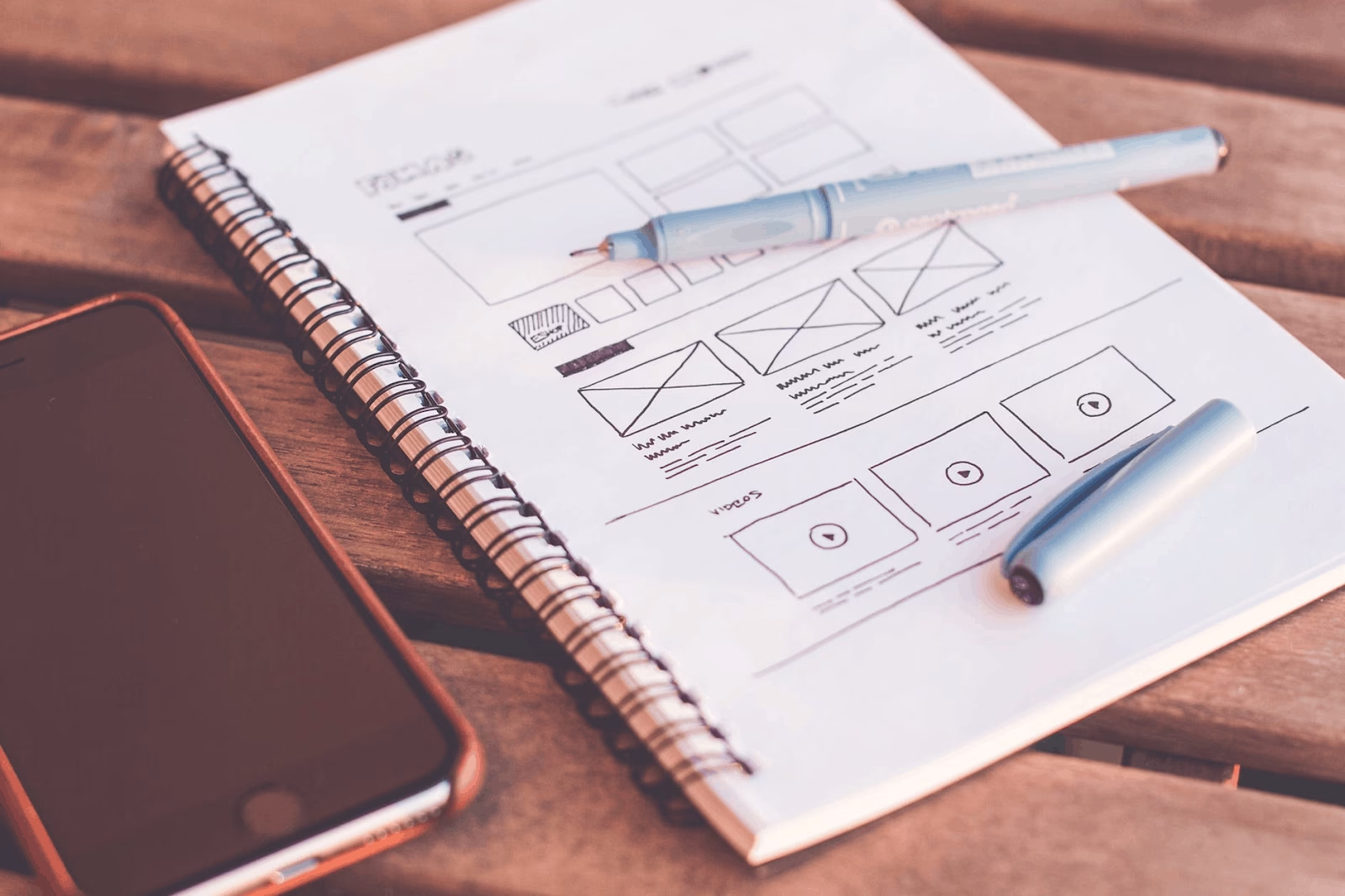
A wireframe can act as a blueprint for your web or app design project. By using a wireframe, you’ll be able to map out important details before you begin designing, ensuring that everyone on the team is able to see your design first hand before they add their own details.
With a roadmap of how you want the design to look and function, the later details such as graphics will be more easily added, thus saving the team time and making the entire project more efficient and cost-effective.
A roadmap for your projects will increase the team’s productivity and cooperation, and ensure that the team is aware of client expectations and what the project should look like once it’s completed.
2. Client Satisfaction
When clients are unsatisfied with your work, you have to go back and edit to make the changes they are asking for. That means taking an already completed project and spending more time on it because specific edits have been requested by the client.
Edits are not cost-effective. Every minute spent on editing is money falling right out of your pocket. That’s what makes wireframes such great tools for ensuring client satisfaction. You can keep the client informed throughout the design process and edit on-the-fly.
Be sure to include your clients by showing them your wireframe at each step of the design process. Once your wireframe is completed and you’re ready to move on, be sure to sit down with the client and explain the functionality of the website or app via the wireframe.
Be sure the client is satisfied with the organization of site elements and how the site navigates before moving onto the next step in the process. Remember that a happy client is much easier to work with and can save you those costly edits later on.
Let’s be honest, sometimes clients expect quite a lot from their projects, and while we admire their ambition, it can be difficult to keep up with their demands. Using a wireframe puts you ahead of the game by keeping the client just as informed as the rest of the team.
3. Exploring Multiple Options
The great thing about wireframes is their versatility. Think of a wireframe as a sort of sketch for your project, that you can edit as you go. This allows you to explore different design and functionality options. You may even find a certain element that you can utilize to save time in the entire process.
Exploring different options is always a good idea, because even though the old adage “if it isn’t broken, don’t fix it” holds some truth, sometimes the “old” way of doing things can become time-consuming as technology advances.
Don’t be afraid to explore different design options via wireframe. The best wireframe tools offer drag and drop interfaces, so trying something new is as simple as dragging a new element onto the project, and then deleting or saving it once you decide if it works for the project.
4. User Experience
When you’re designing any sort of digital medium, user experience should be your first concern. The users will want a simple interface that’s easy to navigate, read, and the tools the website or app offers are easy to use.
A wireframe helps you focus on UX early on in the design process, thus saving you time later on. Updates can be as costly as edits, so it’s important to remember UX when you’re designing. The less you have to update or change a project, the more time and money you’ll save.
5. Responsiveness
As websites are accessed through different mediums (tablets, phones, desktops) the site’s responsiveness can change. Sometimes a very responsive desktop site isn’t quite so responsive on a phone or tablet.
Using a wireframe can allow you to design and test a website across different mediums, and iron out the details on the site’s responsiveness before moving to the next step of the design process when it can become costly to redo.
Responsiveness is a big part of UX and can either entice customers to come back to the app or site or become frustrated and simply leave the site.
Conclusion
Saving time on a project can mean saving money as well. Keeping the client happy, remembering UX, and creating a roadmap for the entire project are some of the many benefits a good wireframe can offer. Remember that a wireframe is always easier to edit than your final design, and it’s better to make edits on-the-fly than after the project is finalized in terms of cost.
Time is money! Clients can be demanding, but always remember that they’re the ones paying for the project, and if they’re not satisfied with your work, you could lose valuable contacts. Use a wireframe to both keep the client informed and gain a better understanding of what they want in future projects.